Advanced Malware Sandbox Market Analysis
Advanced Malware Sandbox Market Analysis
“Must Have” Security Technology Reaches Mass Adoption
RELEASE DATE
09-Sep-2016
09-Sep-2016
REGION
Global
Global
Research Code: K083-01-00-00-00
SKU: IT03136-GL-MR_19004
$4,950.00
Special Price $3,712.50 save 25 %
In stock
SKU
IT03136-GL-MR_19004
Description
Malware has evolved to evade traditional security tools that rely on simple signature-matching for detection. Many of the largest companies in the world have been breached by advanced malware and the problem is only becoming more widespread. In response, sandbox analysis technologies have proven to be a more reliable and accurate approach to detect and block new and advanced (elusive and evasive) malware. As a result, the advanced malware sandbox market has grown precipitously in recent years. While demand for the new technology remains sky high, the market faces a number of challenges in coming years.
RESEARCH: INFOGRAPHIC
This infographic presents a brief overview of the research, and highlights the key topics discussed in it.Click image to view it in full size
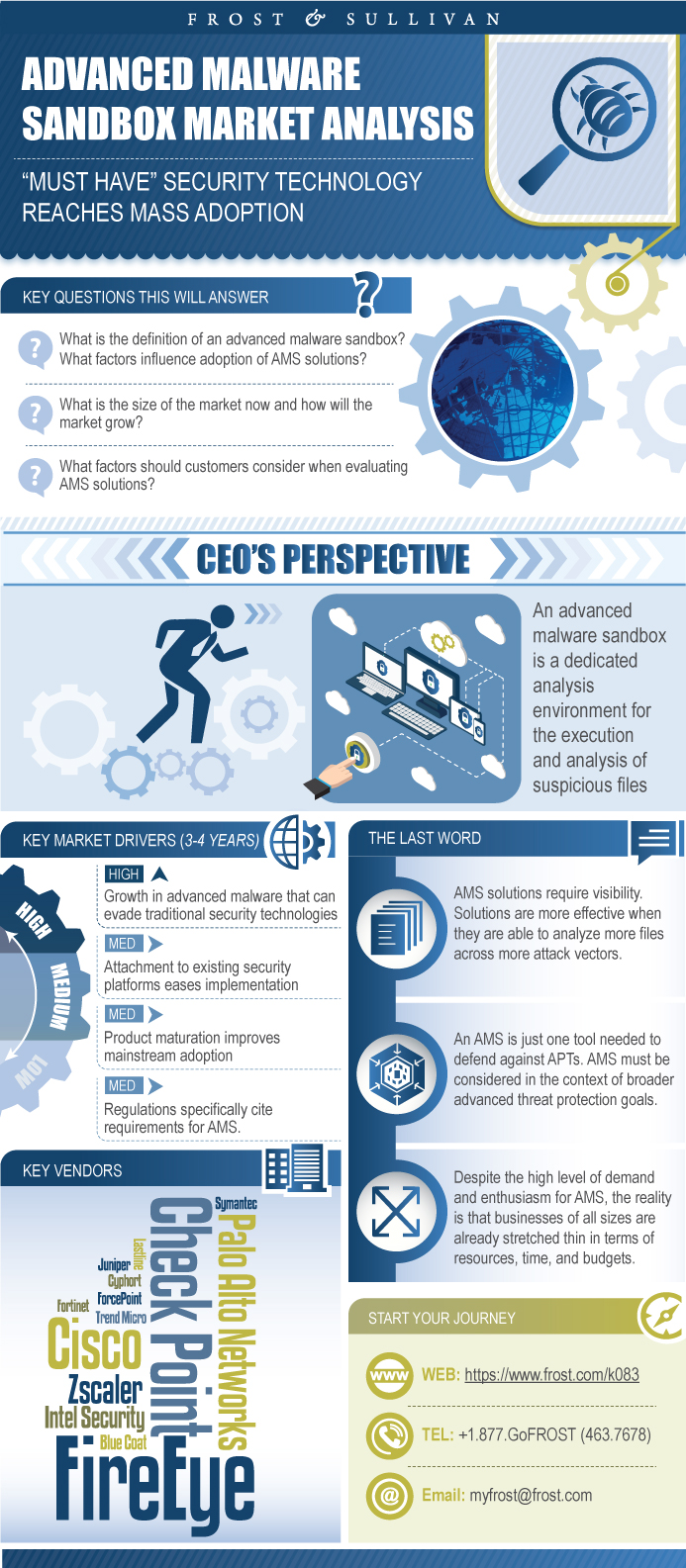
Table of Contents
Key Findings
Market Engineering Measurements
CEO’s Perspective
Introduction to the Research
Key Questions This Study Will Answer
Advanced Malware Sandbox—Market Definitions
Advanced Malware Sandbox—Market Definitions (continued)
Advanced Malware Sandbox—Market Definitions (continued)
Advanced Malware Sandbox—Market Definitions (continued)
Advanced Malware Sandbox—Market Overview
Advanced Malware Sandbox—Market Overview (continued)
Advanced Malware Sandbox—Market Overview (continued)
Advanced Malware Sandbox—Market Overview (continued)
Key Characteristics of an Advanced Malware Sandbox Solution
Key Characteristics of an Advanced Malware Sandbox Solution (continued)
Key Characteristics of an Advanced Malware Sandbox Solution (continued)
Key Characteristics of an Advanced Malware Sandbox Solution (continued)
Key Characteristics of an Advanced Malware Sandbox Solution (continued)
Key Characteristics of an Advanced Malware Sandbox Solution (continued)
Key Characteristics of an Advanced Malware Sandbox Solution (continued)
Key Characteristics of an Advanced Malware Sandbox Solution (continued)
Key Characteristics of an Advanced Malware Sandbox Solution (continued)
Key Characteristics of an Advanced Malware Sandbox Solution (continued)
Key Characteristics of an Advanced Malware Sandbox Solution (continued)
Advanced Malware Sandbox in the Context of Advanced Threat Protection
Advanced Malware in the Context of Advanced Persistent Threats
Advanced Malware in the Context of Advanced Persistent Threats (continued)
Advanced Malware in the Context of Advanced Persistent Threats (continued)
Advanced Malware in the Context of Advanced Persistent Threats (continued)
Advanced Malware in the Context of Advanced Persistent Threats (continued)
Advanced Malware in the Context of Advanced Persistent Threats (continued)
Focus on Advanced Malware to Defend Against Advanced Persistent Threats
Focus on Advanced Malware to Defend Against Advanced Persistent Threats (continued)
Customer Considerations
Customer Considerations (continued)
Drivers and Restraints
Drivers Explained
Drivers Explained (continued)
Drivers Explained (continued)
Drivers Explained (continued)
Drivers Explained (continued)
Drivers Explained (continued)
Restraints Explained
Restraints Explained (continued)
Restraints Explained (continued)
Restraints Explained (continued)
Forecast Assumptions
Revenue Forecast
Revenue and Units Forecast
Revenue and Units Forecast Discussion
Pricing Forecast
Pricing Forecast by Segment
Pricing Forecast Discussion
Percent Revenue Forecast by Segment
Percent Revenue Forecast by Segment Discussion
Percent Revenue Forecast by Segment Discussion (continued)
Percent Revenue Forecast by Region
Revenue Forecast by Region
Percent Revenue Forecast by Region Discussion
Percent Revenue Forecast by Size of Business
Revenue Forecast by Size of Business
Percent Revenue Forecast by Size of Business Discussion
Percent Revenue Forecast by Size of Business Discussion (continued)
Percent Revenue Forecast by Vertical
Revenue Forecast by Vertical
Vertical Market Revenue Forecast Discussion
Percent Revenue Forecast by Distribution Channel
Revenue Forecast by Distribution Channel
Percent Revenue Forecast by Distribution Channel Discussion
Competitive Environment
Competitive Landscape
Competitive Landscape Methodology
Competitive Analysis—Market Share
Competitive Analysis—Market Share (continued)
Competitive Analysis—Solution Capabilities Methodology
Competitive Analysis—Solution Capabilities
Competitive Analysis—Solution Capabilities Competitive Factors
Competitive Analysis—Solution Capabilities Competitive Factors Explained
Competitive Analysis—Solution Capabilities Competitive Factors Explained (continued)
Competitive Analysis—Solution Capabilities Competitive Factors Explained (continued)
Competitive Analysis—Solution Capabilities Competitive Factors Explained (continued)
Appliance Market Segment—Revenue and Units Forecast Discussion
Appliance Market Segment—Revenue and Units Forecast
Appliance Market Segment—Revenue and Units Forecast Discussion
Appliance Market Segment—Pricing
Appliance Market Segment—Pricing Discussion
Appliance Market Segment—Percent Revenue Forecast by Size of Business
Appliance Market Segment—Percent Revenue Forecast by Size of Business Discussion
Appliance Market Segment—Competitive Environment
Appliance Market Segment—Market Share
Software Market Segment—Revenue and Units Forecast Discussion
Software Market Segment—Revenue and Units Forecast
Software Market Segment—Revenue and Units Forecast Discussion
Software Market Segment—Pricing
Software Market Segment—Pricing Discussion
Software Market Segment—Percent Revenue Forecast by Size of Business
Software Market Segment—Percent Revenue Forecast by Size of Business Discussion
Software Market Segment—Competitive Environment
Software Market Segment—Market Share
Cloud Market Segment—Revenue and Units Forecast Discussion
Cloud Market Segment—Revenue and Units Forecast
Cloud Market Segment—Revenue and Units Forecast Discussion
Cloud Market Segment—Pricing
Cloud Market Segment—Pricing Discussion
Cloud Market Segment—Percent Revenue Forecast by Size of Business
Cloud Market Segment—Percent Revenue Forecast by Size of Business Discussion
Cloud Market Segment—Competitive Environment
Cloud Market Segment—Market Share
Predictions
Recommendations
Legal Disclaimer
Vendor Profile: Blue Coat
Vendor Profile: Blue Coat (continued)
Vendor Profile: Blue Coat (continued)
Vendor Profile: Blue Coat (continued)
Vendor Profile: Blue Coat (continued)
Vendor Profile: Blue Coat (continued)
Vendor Profile: Check Point
Vendor Profile: Check Point (continued)
Vendor Profile: Check Point (continued)
Vendor Profile: Check Point (continued)
Vendor Profile: Check Point (continued)
Vendor Profile: Cisco
Vendor Profile: Cisco (continued)
Vendor Profile: Cisco (continued)
Vendor Profile: Cisco (continued)
Vendor Profile: Cisco (continued)
Vendor Profile: Cyphort
Vendor Profile: Cyphort (continued)
Vendor Profile: Cyphort (continued)
Vendor Profile: Cyphort (continued)
Vendor Profile: Dell SonicWALL
Vendor Profile: Dell SonicWALL (continued)
Vendor Profile: Dell SonicWALL (continued)
Vendor Profile: Dell SonicWALL (continued)
Vendor Profile: FireEye
Vendor Profile: FireEye (continued)
Vendor Profile: FireEye (continued)
Vendor Profile: FireEye (continued)
Vendor Profile: FireEye (continued)
Vendor Profile: FireEye (continued)
Vendor Profile: FireEye (continued)
Vendor Profile: Forcepoint
Vendor Profile: Forcepoint (continued)
Vendor Profile: Forcepoint (continued)
Vendor Profile: Fortinet
Vendor Profile: Fortinet (continued)
Vendor Profile: Fortinet (continued)
Vendor Profile: Fortinet (continued)
Vendor Profile: Fortinet (continued)
Vendor Profile: Intel Security
Vendor Profile: Intel Security (continued)
Vendor Profile: Intel Security (continued)
Vendor Profile: Intel Security (continued)
Vendor Profile: Juniper Networks
Vendor Profile: Juniper Networks (continued)
Vendor Profile: Juniper Networks (continued)
Vendor Profile: Juniper Networks (continued)
Vendor Profile: Lastline
Vendor Profile: Lastline (continued)
Vendor Profile: Lastline (continued)
Vendor Profile: Lastline (continued)
Vendor Profile: Lastline (continued)
Vendor Profile: Palo Alto Networks
Vendor Profile: Palo Alto Networks (continued)
Vendor Profile: Palo Alto Networks (continued)
Vendor Profile: Trend Micro
Vendor Profile: Trend Micro (continued)
Vendor Profile: Trend Micro (continued)
Vendor Profile: Trend Micro (continued)
Vendor Profile: Zscaler
Vendor Profile: Zscaler (continued)
Vendor Profile: Zscaler (continued)
Vendor Profile: Zscaler (continued)
Market Engineering Methodology
Market Engineering Measurements
Additional Sources of Information on Study Topic Area
List of Companies Included in “Others”
Partial List of Companies Interviewed
Learn More—Next Steps
List of Exhibits
List of Exhibits (continued)
List of Exhibits (continued)
Popular Topics
Malware has evolved to evade traditional security tools that rely on simple signature-matching for detection. Many of the largest companies in the world have been breached by advanced malware and the problem is only becoming more widespread. In response, sandbox analysis technologies have proven to be a more reliable and accurate approach to detect and block new and advanced (elusive and evasive) malware. As a result, the advanced malware sandbox market has grown precipitously in recent years. While demand for the new technology remains sky high, the market faces a number of challenges in coming years.
| No Index | No |
|---|---|
| Podcast | No |
| Author | Chris Rodriguez |
| Industries | Information Technology |
| WIP Number | K083-01-00-00-00 |
| Is Prebook | No |
 USD
USD GBP
GBP CNY
CNY EUR
EUR INR
INR JPY
JPY MYR
MYR ZAR
ZAR KRW
KRW THB
THB