Changing Dynamics in Healthcare Cybersecurity
Changing Dynamics in Healthcare Cybersecurity
Imperative for Protecting Patient Information Driving Need for New Solutions
08-Jun-2016
North America
Market Research
Description
This research takes into account changing dynamics in the hospital environment, particular to the rise of the Internet of Medical Things and connected medical devices. Cyberattacks related to criminal fraud and abuse as well as data breaches have increased significantly within the healthcare industry from the past few years, and portend specific risks for hospital based medical technologies that increasingly are required to support connected functionalities. Healthcare organizations are now implementing security services aimed at finding the right balance between controlling security costs, deterring attacks, and promoting a productive work environment. Newer cybersecurity solutions from innovative participants ranging from IT governance and risk compliance to threat detection and healthcare fraud and identity protection are augmenting security in the healthcare industry. As the industry moves forward, there are specific precautions and strategies that developers must consider as they deploy their interoperable medical systems.
RESEARCH: INFOGRAPHIC
This infographic presents a brief overview of the research, and highlights the key topics discussed in it.Click image to view it in full size
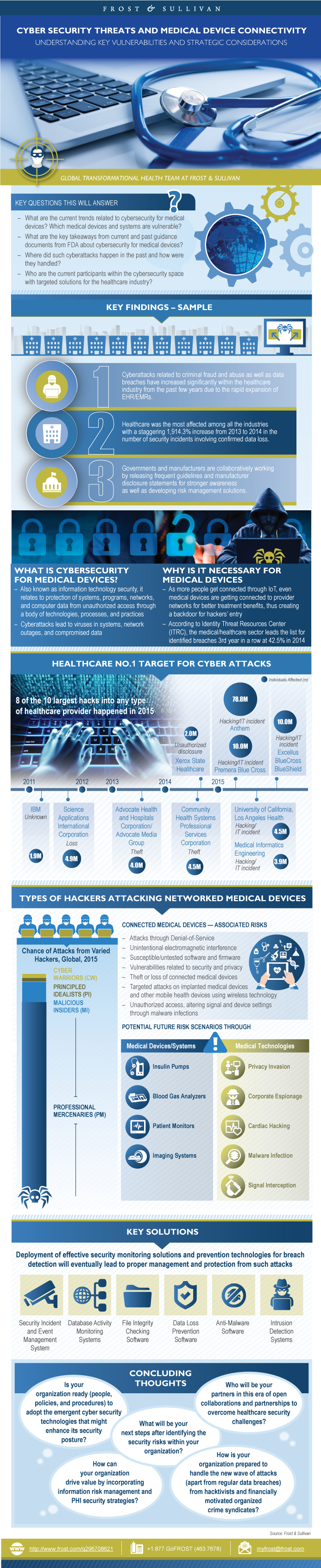
Table of Contents
Executive Summary—Key Findings
Research Scope
The Key Questions that this Study will Answer
What is Cybersecurity for Medical Devices?
Types of Hackers Attacking Networked Medical Devices
Hospital with Vulnerable Medical Devices/Systems
Potential Future Risk Scenarios through Use of Medical Devices/Systems
Connected Medical Devices—Associated Risks
Why Invest Additional Time and Money on Cybersecurity for Networked Medical Devices?
Potential Future Risk Scenarios/Implications through Medical Technologies
Social Engineering—A (new) Way of Hacking a Hospital
Social Engineering—Case Study: Social Media
Social Engineering—Case Study: Hospital Premises
Social Engineering—Case Study: Whaling (CEO Fraud)
Past Attacks
Past Attacks—Medtronic
Past Attacks—St. Joseph Health System
Past Attacks—Anthem
Past Attacks—Hollywood Presbyterian Medical Center
Key Takeaways from these Attacks
Key Takeaways from the Verizon Data Breach Investigations (DBIR) Report—2014 and 2015s
Key Takeaways from the Verizon Data Breach Investigations (DBIR) Report—2014 and 2015s (continued)
Key Takeaways from the Verizon Data Breach Investigations (DBIR) Report—2014 and 2015s (continued)
Key Takeaways from the Verizon Data Breach Investigations (DBIR) Report—2014 and 2015s (continued)
FDA’s Draft Guidance on Premarket Submissions for Cybersecurity Risks in Medical Devices—Key Takeaways
FDA’s Draft Guidance on Postmarket Management of Cybersecurity Risks in Medical Devices—Key Takeaways
Initiatives from the Government and Industry toward Medical Device Security
News Affairs—Trend Lines Overs the Years
Hot Cybersecurity Companies to Watch in 2016 for the Healthcare Industry
Hot Cybersecurity Companies to Watch in 2016 for the Healthcare Industry (continued)
Clearwater Compliance
Nexusguard
DB Networks
TraceSecurity
Coalfire Systems
Recommendations for the Medical Device Manufacturers
Recommendations for the Healthcare Organization
Recommendations—For the Industry and Hospitals
Key Conclusions
Concluding Thoughts
Legal Disclaimer
The Frost & Sullivan Story
Value Proposition: Future of Your Company & Career
Global Perspective
Industry Convergence
360º Research Perspective
Implementation Excellence
Our Blue Ocean Strategy
Popular Topics
| Deliverable Type | Market Research |
|---|---|
| No Index | No |
| Podcast | No |
| Author | Harpreet Singh Buttar |
| Industries | Healthcare |
| WIP Number | 9AB9-00-47-00-00 |
| Is Prebook | No |