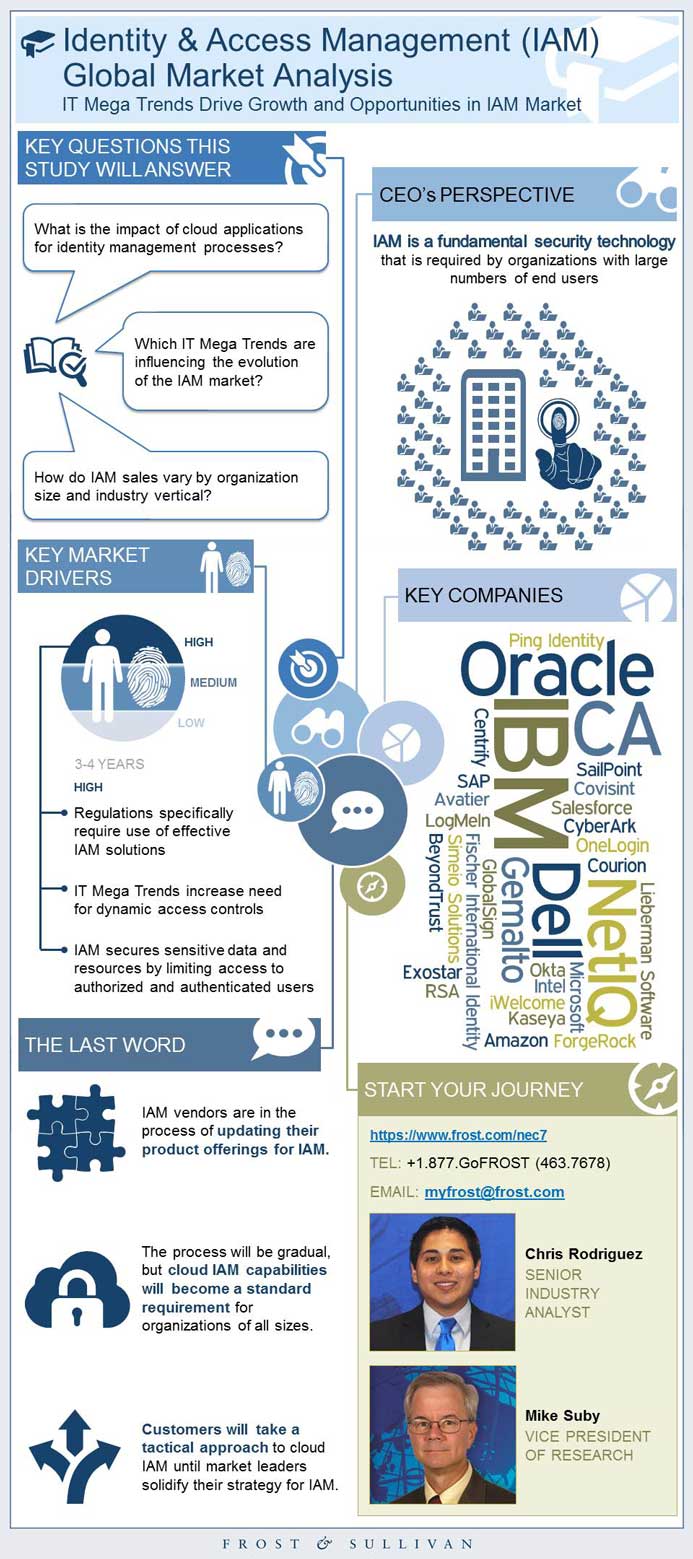
Identity & Access Management (IAM) Global Market Analysis
Identity & Access Management (IAM) Global Market Analysis
IT Mega Trends Drive Growth and Opportunities in IAM Market
RELEASE DATE
05-Feb-2015
05-Feb-2015
REGION
North America
North America
Deliverable Type
Market Research
Market Research
Research Code: NEC7-01-00-00-00
SKU: IT00757-NA-MR_02047
$4,950.00
In stock
SKU
IT00757-NA-MR_02047
Description
Identity and access management (IAM) is the process of identification, authentication, authorization, and administration of digital users. IAM solutions are widely used by large businesses and enterprise organizations to manage thousands of user identities. However in recent years, information technology (IT) Mega Trends such as mass smartphone adoption and cloud services have changed how organizations manage identity and access requirements. Changing IT practices create demand for new IAM solutions and generate opportunities for growth by innovative companies.
RESEARCH: INFOGRAPHIC
This infographic presents a brief overview of the research, and highlights the key topics discussed in it.Click image to view it in full size
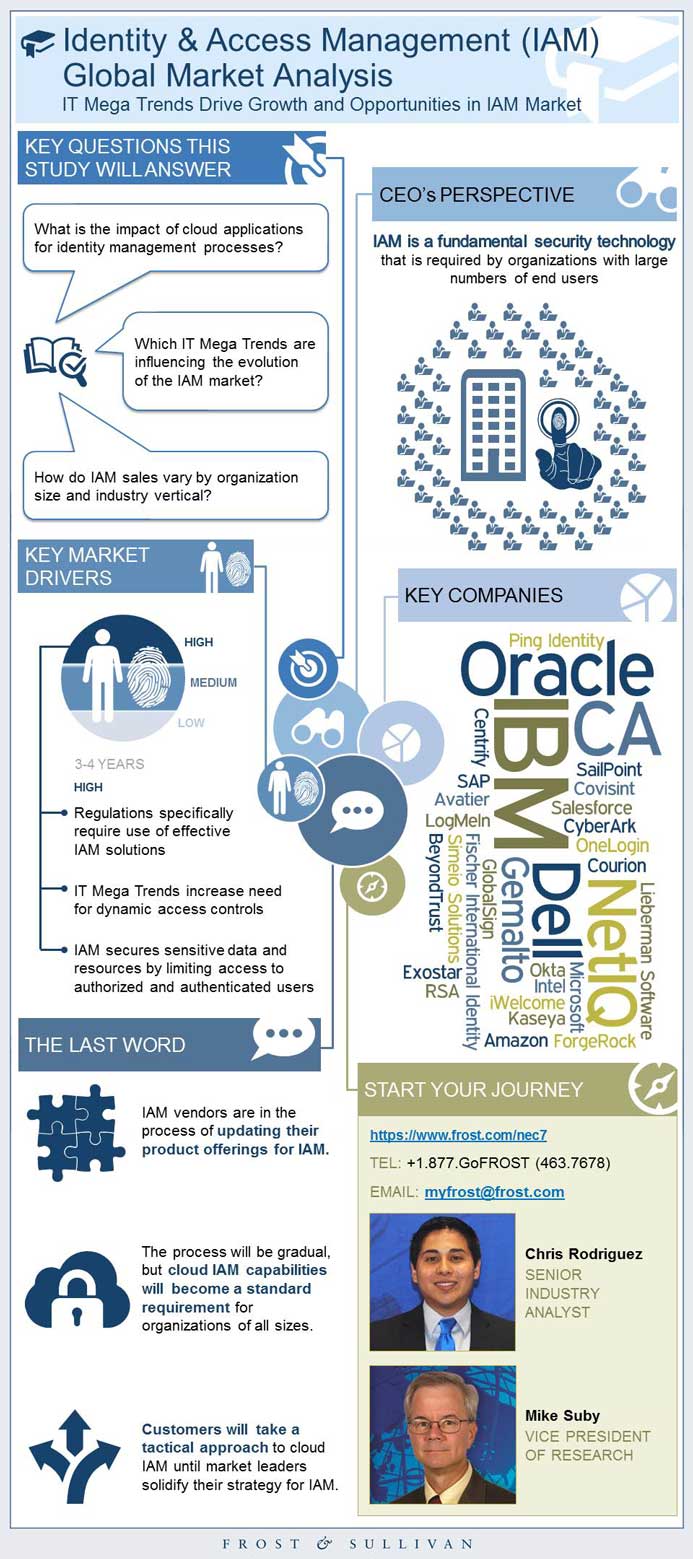
Table of Contents
Executive Summary
Market Engineering Measurements
Market Engineering Measurements (continued)
CEO’s Perspective
Introduction to the Research
Key Questions This Study Will Answer
Market Overview
Market Overview (continued)
Market Overview (continued)
Market Overview (continued)
Definitions
Definitions (continued)
Definitions (continued)
Definitions (continued)
Definitions (continued)
Drivers and Restraints
Drivers Explained
Drivers Explained (continued)
Drivers Explained (continued)
Drivers Explained (continued)
Drivers Explained (continued)
Drivers Explained (continued)
Drivers Explained (continued)
Drivers Explained (continued)
Restraints Explained
Restraints Explained (continued)
Restraints Explained (continued)
Restraints Explained (continued)
Forecast Assumptions
Revenue Forecast
Unit Shipment and Revenue Forecast Discussion
Unit Shipment and Revenue Forecast Discussion (continued)
Pricing Trends and Forecast
Pricing Trends and Forecast Discussion
Percent Revenue Forecast by Segment
Segment Percent Revenue Forecast Discussion
Segment Percent Revenue Forecast Discussion (continued)
Percent Revenue Forecast by Distribution Channel
Distribution Channel Discussion
Percent Revenue Forecast by Region
Regional Percent Revenue Forecast Discussion
Revenue Forecast by Vertical Market
Vertical Market Revenue Forecast Discussion
Percent Revenue Forecast by Customer Size
Customer Size Percent Revenue Forecast Discussion
Customer Size Percent Revenue Forecast Discussion (continued)
Percent Revenue Forecast by Horizontal Segment
Horizontal Segment Percent Revenue Forecast Discussion
Horizontal Segment Percent Revenue Forecast Discussion (continued)
Market Share
Competitive Environment
Competitive Environment Discussion
Competitive Environment Discussion (continued)
Competitive Environment Discussion (continued)
Competitive Factors and Assessment
Competitive Factors and Assessment (continued)
Competitive Factors and Assessment (continued)
Software Segment Breakdown
Software Segment—Market Engineering Measurements
Software Segment—Revenue Forecast
Software Segment—Revenue Forecast Discussion
Software Segment—Revenue Forecast Discussion (continued)
Software Segment—Market Share
Software Segment—Competitive Environment
Cloud Segment Breakdown
Cloud Segment—Market Engineering Measurements
Cloud Segment—Revenue Forecast
Cloud Segment—Revenue Forecast Discussion
Cloud Segment—Revenue Forecast Discussion (continued)
Cloud Segment—Market Share
Cloud Segment—Competitive Environment
The Last Word—Predictions
The Last Word—Recommendations
Legal Disclaimer
Vendor Profile: Avatier
Vendor Profile: Avatier (continued)
Vendor Profile: BeyondTrust
Vendor Profile: BeyondTrust (continued)
Vendor Profile: BeyondTrust (continued)
Vendor Profile: Centrify
Vendor Profile: Centrify (continued)
Vendor Profile: Centrify (continued)
Vendor Profile: IBM
Vendor Profile: IBM (continued)
Vendor Profile: Intel Security (formerly McAfee)
Vendor Profile: Intel Security (formerly McAfee) (continued)
Vendor Profile: LogMeIn
Vendor Profile: LogMeIn (continued)
Vendor Profile: NetIQ
Vendor Profile: NetIQ (continued)
Vendor Profile: Okta
Vendor Profile: Okta (continued)
Vendor Profile: RSA
Vendor Profile: RSA (continued)
Vendor Profile: SailPoint
Vendor Profile: SailPoint (continued)
Vendor Profile: SailPoint (continued)
Market Engineering Methodology
Market Engineering Measurements
Market Engineering Measurements (continued)
Additional Sources of Information on Study Topic Area
Partial List of Companies Interviewed
Partial List of Companies Included in “Others”
Learn More—Next Steps
Popular Topics
Identity and access management (IAM) is the process of identification, authentication, authorization, and administration of digital users. IAM solutions are widely used by large businesses and enterprise organizations to manage thousands of user identities. However in recent years, information technology (IT) Mega Trends such as mass smartphone adoption and cloud services have changed how organizations manage identity and access requirements. Changing IT practices create demand for new IAM solutions and generate opportunities for growth by innovative companies. --BEGIN PROMO-- 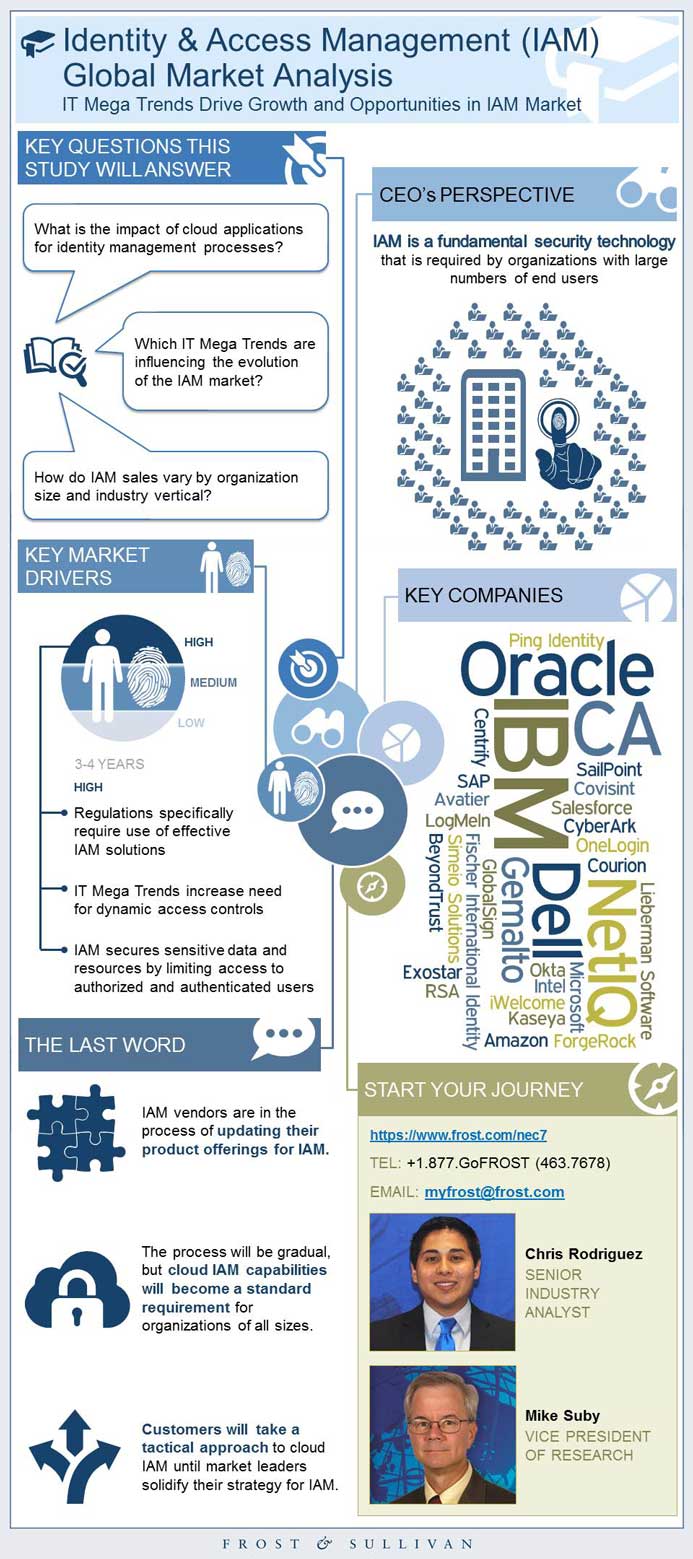
| Deliverable Type | Market Research |
|---|---|
| No Index | No |
| Podcast | No |
| Author | Chris Rodriguez |
| Industries | Information Technology |
| WIP Number | NEC7-01-00-00-00 |
| Is Prebook | No |