Network Security
Cybersecurity has become an extremely relevant and pressing issue with the passing of time, and is only about to increase in importance. All organizations have sensitive data that needs to be protected to maintain the organization’s edge in technology, IP, business innovation and most importantly, their customers. Virtually every industry, from banking/financial services, telecommunications, healthcare, technology, retail, manufacturing services, and public sector either have or critically need to have network security solutions in place to protect their networks and systems from internal or external harm.
Frost & Sullivan’s Information Technology research and consulting programs look at conventional and unconventional technologies, with specific focus on top-level potential disruptors such as cybersecurity, artificial intelligence, machine learning, and IOT or the Internet of Things. In the Network Security market, we look at, among other segments:
- Infrastructure Security
- Endpoint Security
- Managed Security Services
- Access Control
- Vulnerability Research
We work closely with the world’s largest IT firms and upcoming disruptive start-ups to predict macro and micro trends related to products, services, technology and business models that can define growth. Tailored, customized solutions provide clients with the best strategies for growth, supported by the right key data points researched to meet the client’s needs and the specific engagement. Our research spans broadly across the sector and provides deep insights into specific markets in the most significant areas of IT and the IT industry.
-
23 Nov 2015 | Asia Pacific
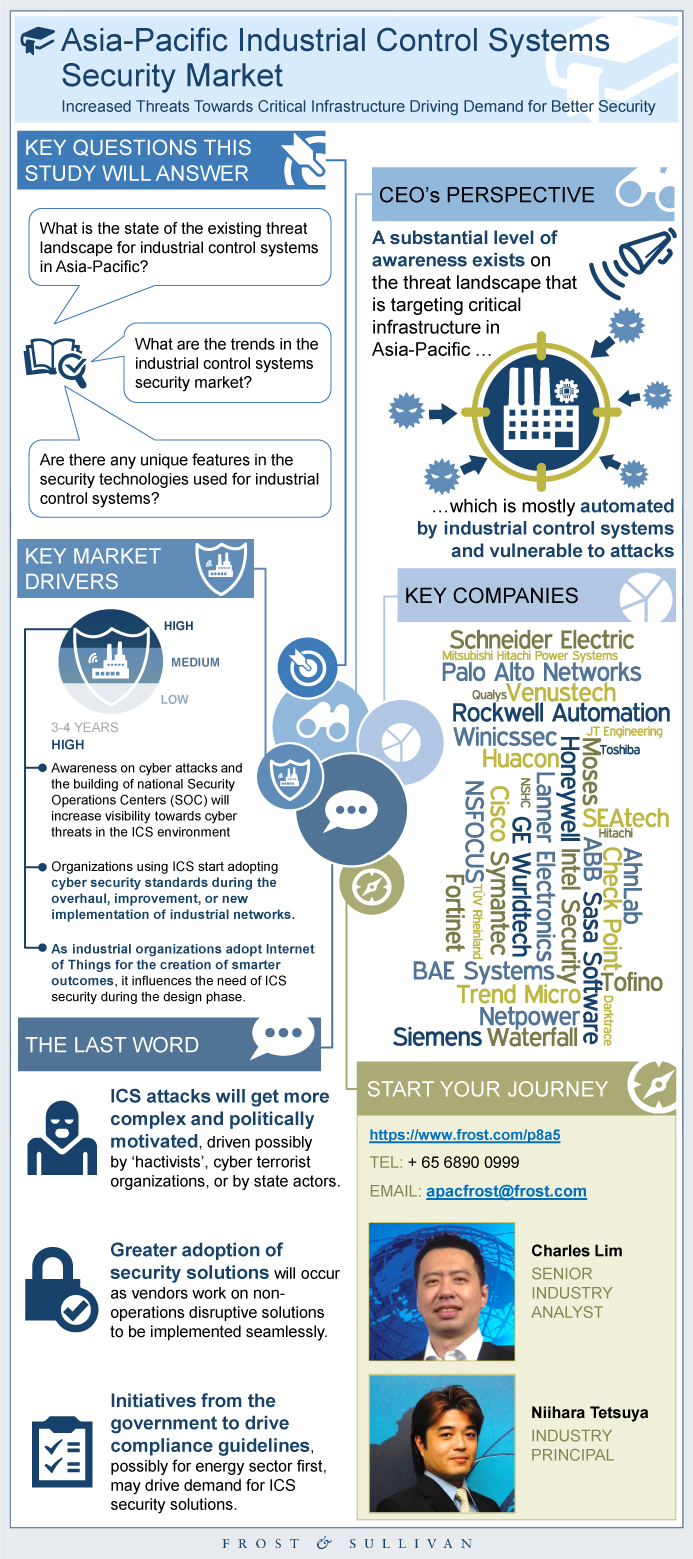
Asia-Pacific Industrial Control Systems Security Market
Increased Threats Towards Critical Infrastructure Driving Demand for Better Security
The study analyzes the Asia-Pacific industrial control systems (ICS) security market. In the 2010s, there were notable targeted attacks such as Stuxnet that attacked centrifuges, followed by a slew of attacks with code names such as Aurora, Flame, and Havex, discovered by various security vendors’ threat research and intelligence centers. The dri...
$13,500.00 -
20 Nov 2015 | North America
Network Security Forensics Global Market
How Much Forensics Do You Need?
When a security breach occurs, an investigation needs to be initiated. Network security forensics is the technology used not only to understand the nature of the breach, but also to trigger the beginning of remediation. Traditional network security platforms include event correlation and full packet capture. However, different security approaches i...
$4,950.00 -
12 Nov 2015 | Global
Public Vulnerability Research Market in 2014
The Evolving Threat Environment During the Internet of Things Era
The Frost & Sullivan analysis of the global public vulnerability research market in 2014 is part of a series of studies compiled from various public sources to analyze the public vulnerability landscape from 2013 to 2014. Vulnerability data is collected, queried, and segmented, resulting in a wealth of information that is intended to provide qualit...
$2,450.00 -
02 Nov 2015 | North America
DDoS Mitigation Global Market Analysis
New Solutions Accelerate Market Growth
Distributed denial-of-service (DDoS) is an increasingly popular method of cyber attack. DDoS attacks disrupt operations and block access for legitimate end users, customers, and employees, causing missed sales opportunities, end user frustration, service degradation, and embarrassment for targeted organizations. Attacks are growing in volume, sophi...
$4,950.00 -
30 Sep 2015 | North America
Managed Security Services in North America
Attention Moves from the Perimeter to the Endpoint and the Network
This report provides an analysis of the market for the North American managed security services market. These network security services include some degree of proactive monitoring of the customer’s security environment, and may encompass protection against denial of service attacks, email viruses/worms, spam, and other various cyber maladies. Thi...
$4,950.00 -
26 Aug 2015 | North America
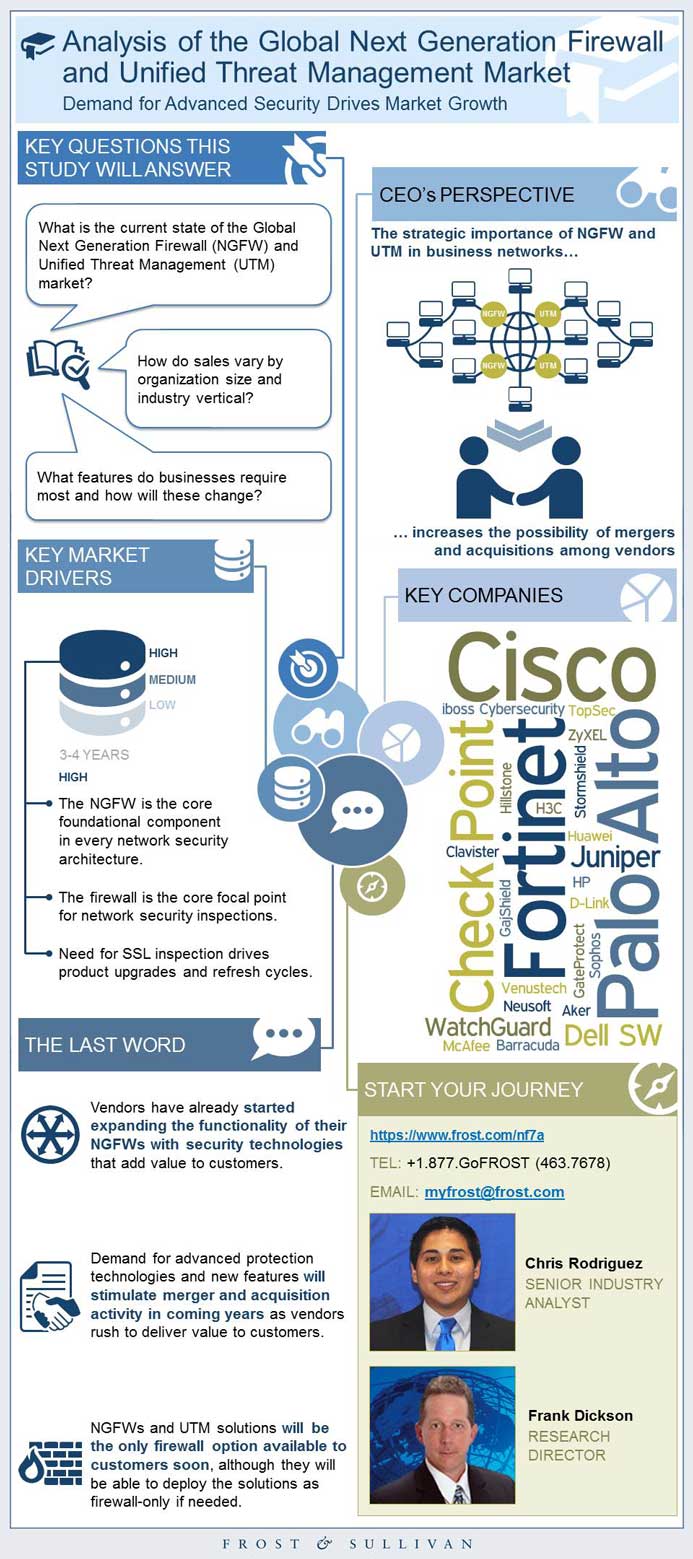
Analysis of the Global Next Generation Firewall and Unified Threat Management Market
Demand for Advanced Security Drives Market Growth
NGFW and UTM solutions provide essential control and inspection of inter-network communications at important network boundaries. Vendors are continually adding cutting-edge security technologies to address rapidly changing threats and emerging technologies that increase risk in organizations of all sizes. Demand for NGFW and UTM capabilities shows ...
$4,950.00 -
29 Jul 2015 | Global
Vulnerability Management (VM) - Global Market Analysis
The Plan Beyond the Scan
Vulnerability management (VM) is a perimeter based cyber defense that scans network infrastructures and identifies and prioritizes critical security issues. IP scanning is a foundational network security approach; however, the leading VM vendors are adding endpoint visibility, network mapping, web application scanning, and continuous monitoring to ...
$4,950.00 -
24 Jul 2015 | Asia Pacific
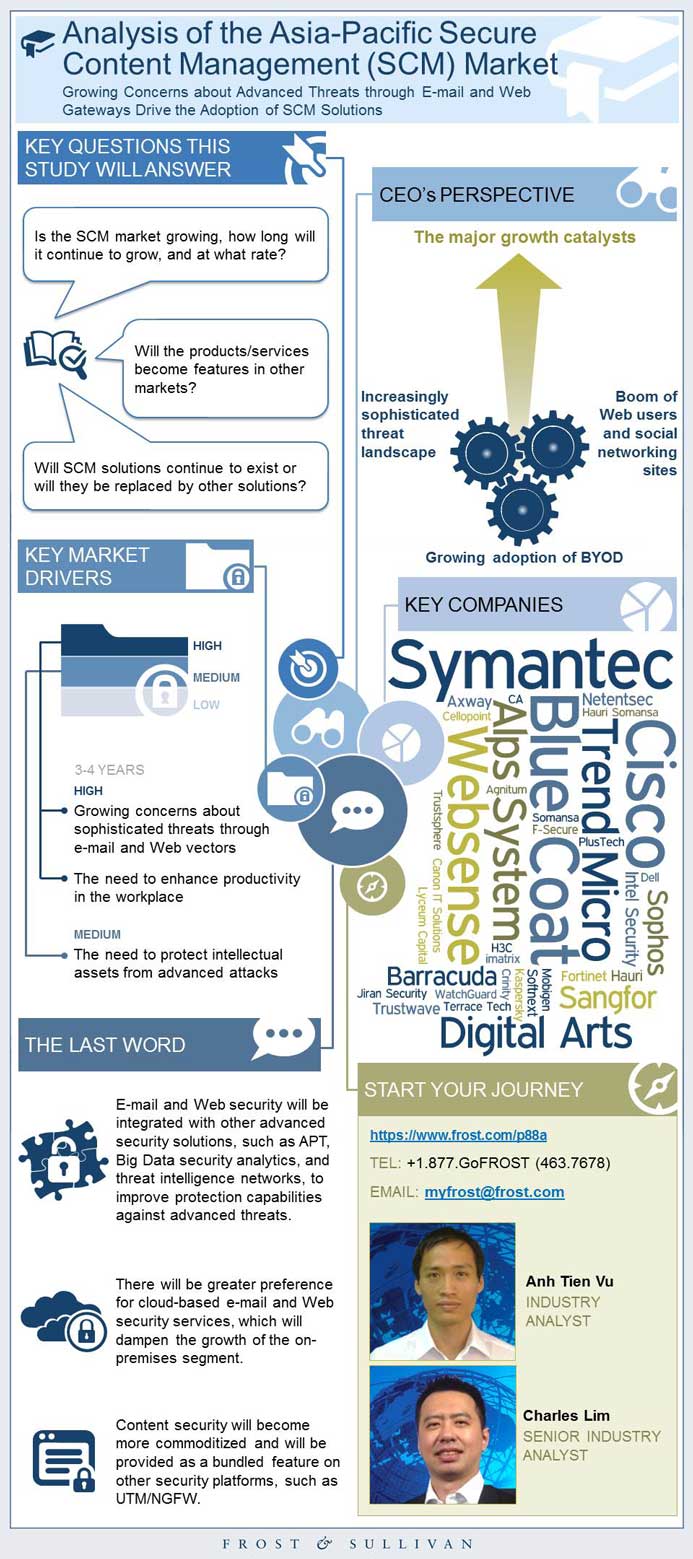
Analysis of the Asia-Pacific Secure Content Management (SCM) Market
Growing Concerns about Advanced Threats through E-mail and Web Gateways Drive the Adoption of SCM Solutions
The Asia-Pacific secure content management (SCM) market comprises e-mail security and Web security. As enterprises continue to spend on security technologies to protect their employees from spamming and phishing e-mails and un-desired and malicious Web URLs, to enhance productivity at the workplace and defend against advanced threats passing throug...
$17,500.00 -
03 Jul 2015 | South Asia, Middle East & North Africa
Network Security Market in India CY 2014
Advanced, Sophisticated, and Targeted Attacks Leads to Higher Adoption of Network Security Solutions
In the last few years, there have been organised security breaches in the Indian subcontinent that have caused data losses worth millions of dollars. Organisations in the region have started to realise that these sophisticated attacks not only affect their business continuity and agility but also tarnish their brand image. Consequently, companies a...
$1,500.00 -
02 Jul 2015 | Asia Pacific
Analysis of the Asia-Pacific Network Security Market 2014
Demands of Prevention, Detection, and Remediation through Network Security
The Asia-Pacific (APAC) network security market recorded a year-on-year growth of 3.6% in 2014. High profile breaches involving key retailers in the United States have led to more enterprises believing there is a need to detect and remediate hidden malware in their networks. Network firewall companies have performed strategic acquisitions, integrat...
$20,000.00
 USD
USD GBP
GBP CNY
CNY EUR
EUR INR
INR JPY
JPY MYR
MYR ZAR
ZAR KRW
KRW THB
THB